Many businesses are at risk of a financial and reputation loss and it will only be a matter of time until most businesses have been attacked. Law enforcement makes a great effort to prevent cybercrime, however many cyber-criminals are located in countries that are not friendly with the USA. Some cyber-criminal activities are state sponsored.

Cyber attacks on businesses are increasing and ransomware especially is increasing exponentially. Unfortunately many businesses do not invest in adequate cybersecurity protection and so when a ransomware attack occurs they are obliged to pay the extortion demand to unlock the business data if they want to continue in business.
Most businesses depend on technology to prosper, using computers to manage information and by doing business using the Internet. Cybersecurity is a necessary part of business technology and the cost must be included in the operating budget. Cybersecurity is not optional; it is as essential as a lock on a door to keep criminals out of a building and a burglar alarm to call the police if the building is invaded.
The situation of ransomware is summed up by a quote from the World Economic Forum, 2022 Report: Ransomware and 'ransom-war'.
"As online working surged during the pandemic, so did cybercrime - ransomware attacks rose 151% in 2021. The World Economic Forum’s Global Cybersecurity Outlook found there were on average 270 cyber-attacks per organization that year, with each successful cyber breach costing a company $3.6m."
A business can be threatened in many ways by cybercriminals through data theft and ransomware.
Data theft; cybercriminals are seeking to exploit or sell stolen information.
Ransomware; a form of extortion where a ransom is demanded to unlock or return business data.
Hospitals continue to be lucrative targets for ransomware groups because of their valuable data and higher rate of paying ransoms. TechTarget Security: 2/22/23.
The cybercriminals objective is to find a way to access to the network data servers and find the business data files. There are two approaches to attack the network.
External threats;
Internal threats;
There are several methods of planting a Trojan virus on a user computer. The methods are used simultaneously and repeated persistently until a user makes a mistake and installs the virus without realizing it. Once the Trojan virus is installed on the user computer the cybercriminal gets full network and server access. Some of the methods are listed below.
Phishing:
Malware:
Credential theft:
Steps of a Trojan virus ransomware attack: see the following diagram:
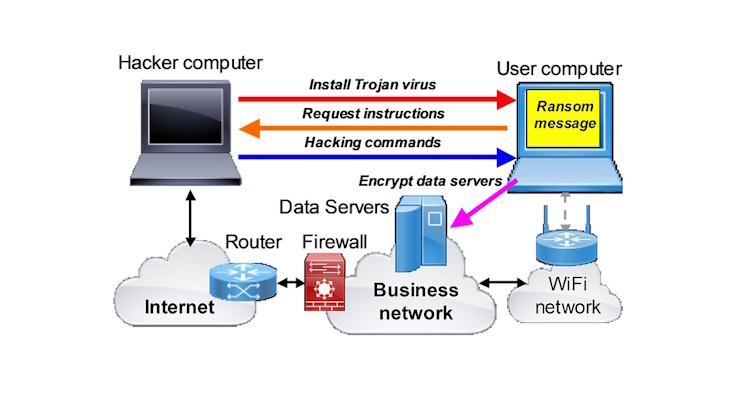
Data breaches are any type of cyber attack where the business data is accessed and stolen by a cybercriminal for financial gain. The criminal may sell the data or use the data to blackmail the business. A data breach might be due to a business or country seeking military or financial secrets.
Ransomware is a method of extortion where the cybercriminal encrypts business data to block access then demands a ransom to unlock the data. In some cases the criminal will also sell the data in addition to collecting a ransom.
All businesses should invest in cybersecurity urgently before they become the next victim of a cybercriminal.
Protecting a business against a cyber attack requires the development and deployment of a comprehensive business cyber-protection plan. The plan has three parts:
Cybersecurity is not a one-time investment but an ongoing process. Computer technology is constantly evolving and cybercriminals are constantly finding new methods to attack a business. A business computer network required constant review (monthly if possible) with frequent updates as software and hardware manufacturers release security updates.
The cybersecurity awareness staff training should include the following points.
It is important to reward staff support for participation with the cybersecurity awareness training and encourage staff to help to identify potential risks.
A tested data recovery plan is essential to prepare for the worst case where the cybercriminal is able to break in to the network and plan ransomware. The recovery plan will permit the business to recover all data files from secure backup storage and continue working without paying the ransom. The recovery plan should include the following entries.
If a cyber attack occurs proceed as follows.
Do not connect the Internet until the cybercriminals point of entry is found. If the network is connected to the Internet the cybercriminal will try to attack the restored system.
The inaccessible offsite backup with a write only encrypted link is important as the cybercriminal will try to encrypt the backup in addition to the business database. The last few backups that were saved may be encrypted.
Technology investments to upgrade the business computer network for the current cybersecurity standards are essential. Standards are evolving continuously as cybercriminals develop new methods and exploit the network and software weak points so the process of upgrading the business network is constant.
Zero trust is a very important security methodology that all business networks should adopt yet few small and medium businesses install it. Zero trust network cybersecurity means never trust, always verify. All devices connect through zero trust cybersecurity which protects business data, software and infrastructure using strict protocols, and monitors network traffic for suspicious behavior or potential threats. Zero trust cybersecurity has four principles that are implemented by an end point firewall.
Zero trust identity verification requires multi-factor authentication (MFA) for network protection. 2-factor authentication is one version of MFA and is the biggest single cyber-criminal deterrent. When cyber-criminals see MFA is in use then most they will likely move on to the next victim.
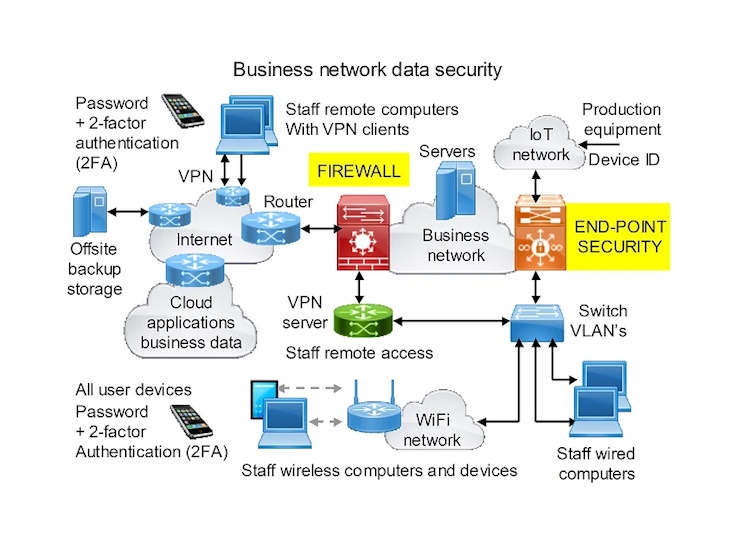
There are a series of network upgrades that will improve the cybersecurity of the business computer network and protect the business data from attack by theft or ransomware. The network upgrades are explained in the following sections.
It is very important to install a firewall between the Internet and the business network as this connection is the first point that the cybercriminal will try to attack the network. There are many firewall products available but all require expert configuration to ensure that the business network is protected.
An important security feature is called zero-trust. This means that user devices are not allowed to connect to the network until the device has been authenticated and the user has been authenticated using multi-factor authentication (MFA). This will reduce the possibility that a device infected with a Trojan virus is connected to the business network. To protect the network users devices should not be permitted to connect to other networks that have no cybersecurity protection. User devices are connected through an end-point firewall that will authenticate devices and users using 2-factor authentication.
The end-point firewall has several important tasks, listed below:
It is important to install anti-virus software on every device that connects to the network and ensure that the anti-virus software is updated with new profiles as they become available.
If the business has staff that connect remotely then the remote access is a weak point that the cybercriminals will attack. Remote connections should only be connected with a VPN and then the remote user should be authenticated with 2FA before being permitted to connect to the network. Password theft is common so 2FA will prevent a stolen password being used even if the criminal gets remote access.
The business should have a secure offsite backup that is only accessible via a server encrypted write batch transaction. If the backup is accessible in the local network the criminal will encrypt that before encrypting the main database.
A good security measure is to use cloud versions of application software as cloud services have good cyber-protection. A custom developed application can be transferred to a service such as AWS or Azure for greater security.
If the business provides open WiFi for guests or visitors a firewall should be installed to isolate the visitor network. This applies to motels, hotels and any retail business that offers free WiFi.
xFinally the network should be checked for IoT (Internet of things) devices that have a connection to the Internet for monitoring or servicing. The IoT device may be a printer or air conditioning controller. IoT devices that are connected to the Internet can be hacked and can give the criminal access to the business databases.
All the business network upgrades that are explained here are shown on the network diagram. A business should call their IT service vendor to request that the computer network is upgraded with these cybersecurity specifications.
Readers are invited to share this information with others. If any reader has a question regarding this information please contact us via our contact page.
Protect your business from an expensive ransomware attack. Unfortunately ransomware attacks have become a ...
A business network requires a number of steps for a full cybersecurity plan. Cyber attacks on businesses ...